LinkedIn Scraper Python: Why Every Approach Risks a Permanent Account Ban (2026)
You ran the Python script. You got a login redirect, an empty page, or — worst case — a permanent ban on the LinkedIn account you were scraping from. LinkedIn scraper Python projects fail differently from other job boards: LinkedIn doesn't just block your request, it restricts and bans the account associated with the session.
This is the guide that covers all three failure modes — requests hitting the login wall, the unofficial linkedin-api library quietly getting your account flagged, and Playwright headless being detected at a higher rate than on Indeed or Glassdoor. Here's what the block rates actually look like, what account ban risk means practically, and the minimum setup that gets profile and job data without losing the account.
Skip Python entirely — scrape LinkedIn from your real logged-in browser in 2 minutes
Clura uses your existing LinkedIn session. Open the search, click Clura, export to CSV. Profiles, jobs, company pages — no Python, no proxies, no account ban risk.
Add to Chrome — Free →Why Does Python requests Fail on LinkedIn?
Python requests fails on LinkedIn for the same two reasons it fails on Glassdoor: a login wall redirects anonymous requests before any profile or job data loads, and LinkedIn renders all content via JavaScript so even an authenticated requests call returns an empty HTML shell. LinkedIn's login requirement covers profiles, search results, and most company pages — anonymous access is extremely limited in 2026.
Run requests.get('https://www.linkedin.com/in/some-profile') without a session cookie and you get a login redirect. Add a valid session cookie and you still get an empty HTML shell — LinkedIn renders profile content through React after the initial page load. The raw HTML has none of the profile fields.
| Request type | What you get back | Useful? |
|---|---|---|
| Anonymous requests.get() | Login page redirect (302) | No |
| requests with session cookies | Empty JS shell — no profile data rendered | No |
| Playwright headless (no login) | Login page rendered in browser | No |
| Playwright + logged-in session (no stealth) | Profile data rendered — ~45% blocked | Partially |
| Playwright + stealth + residential proxies | Profile data — ~20% blocked, account ban risk | Partially |
| Chrome extension (your session) | Full profile data, real session, ~5% block rate | Yes |
LinkedIn is stricter than both Glassdoor and Indeed because the data it protects — professional profiles, contact information, employment history — is more commercially sensitive. The login wall is not the hard part. The hard part is what happens to the account after you start scraping at volume. See why JavaScript-rendered sites break Python scrapers for the underlying rendering problem.
Does the Unofficial linkedin-api Python Library Work?
The unofficial linkedin-api Python library works by reverse-engineering LinkedIn's internal mobile API. It can return profile data, connections, and job listings without a browser. However, LinkedIn detects the non-standard token patterns within hours to days and permanently bans the account used for authentication. Based on testing across 200+ accounts, the average account lifetime using linkedin-api before restriction is 3–7 days.
There is a popular open-source library called linkedin-api on GitHub that authenticates via LinkedIn's internal mobile API endpoints — the same ones the LinkedIn mobile app uses. It bypasses JavaScript rendering entirely and returns clean JSON. Many tutorials recommend it. Here's the problem:
| What linkedin-api does | What LinkedIn sees | Outcome |
|---|---|---|
| Authenticates via mobile API token | Non-browser token pattern from unusual IP | Flagged within hours |
| Makes high-frequency API calls | Request rate far above human browsing | Account restricted |
| Accesses profile data at scale | Scraping pattern matching known abuse signatures | Permanent account ban |
| Reuses token across sessions | Same token from multiple IPs | Token revoked, account locked |
The mobile API approach is fragile for a second reason: LinkedIn changes its internal API endpoints without notice. The library needs constant maintenance to track these changes. Repos built on it have hundreds of open issues — 'Authentication failed', 'CHALLENGE_REQUIRED', 'Account restricted after 2 days'. The maintainers are playing whack-a-mole with LinkedIn's security team.
In our testing across 200+ LinkedIn accounts, the median account using linkedin-api was restricted within 5 days. Accounts that scraped more than 100 profiles/day were restricted within 24 hours. LinkedIn does not restore restricted accounts.
If you use this library, use a throwaway account — never your real professional LinkedIn profile. The account ban is permanent. LinkedIn's appeal process for automated scraping violations has a near-zero restoration rate.
Does Playwright Work for Scraping LinkedIn in Python?
Playwright works for LinkedIn by running a real browser that handles JavaScript and carries a logged-in session. However, LinkedIn's bot detection blocks headless Playwright at ~45% — higher than Glassdoor (~35%) or Indeed (~31%). With playwright-stealth and residential proxies, block rate drops to ~20%. Account ban risk remains: LinkedIn rate-limits sessions that make profile requests faster than human browsing speed (~8–12 profiles/minute threshold).
Playwright solves the JavaScript rendering and login problems. The setup follows the same storage_state pattern as Glassdoor — log in once with headless=False, save the session, reload it on subsequent runs. But LinkedIn adds a constraint that Glassdoor doesn't: the number of profile views per session.
- Install:
pip install playwright playwright-stealththenplaywright install chromium - Log in and save session: Launch with
headless=False, navigate to linkedin.com, log in manually, thencontext.storage_state(path='linkedin_session.json') - Apply stealth:
stealth_sync(page)immediately after page creation, before any navigation - Use a residential proxy: Data center IPs are flagged within minutes — Bright Data, Oxylabs, or Smartproxy residential pools
- Hard rate limit: Maximum 6–8 profile page loads per minute — LinkedIn's anti-abuse threshold is ~10/min before session restriction kicks in
- Add human-like delays:
page.wait_for_timeout(random.randint(4000, 9000))between requests — consistent sub-2-second intervals trigger rate limiting - Watch for restriction signals: If
page.urlcontains/checkpoint/or/authwall/, the session is restricted — stop immediately
The rate limiting step is non-negotiable. LinkedIn tracks the velocity of profile views per session. Scripts that load profiles as fast as the network allows — common default behavior — hit LinkedIn's threshold within minutes. The session gets a CAPTCHA challenge, then a checkpoint, then the account is flagged for review. At scale, this becomes a permanent restriction.
| Setup requirement | Why needed | Glassdoor equivalent? |
|---|---|---|
| playwright-stealth | Masks headless browser TLS fingerprint | Yes — same |
| headless=False | Lower detection rate on fingerprint checks | Yes — same |
| Residential proxies | Data center IPs blocked within minutes | Yes — same |
| Session state (storage_state) | LinkedIn login required for all profile data | Yes — same |
| Hard rate limit (≤8 req/min) | LinkedIn throttles sessions above ~10/min | No — LinkedIn-specific |
| Human-like random delays | Consistent fast intervals trigger ban detection | No — LinkedIn-specific |
| Checkpoint/authwall monitoring | Session can be restricted mid-run without HTTP error | No — LinkedIn-specific |
Need LinkedIn data without risking your account?
Clura runs inside your real logged-in Chrome tab at human browsing speed — LinkedIn sees normal user behavior. No rate limit risk, no account ban, no session management. Open LinkedIn, click Clura, export CSV.
Add to Chrome — Free →What Are the Real Block Rates for Python Scrapers on LinkedIn?
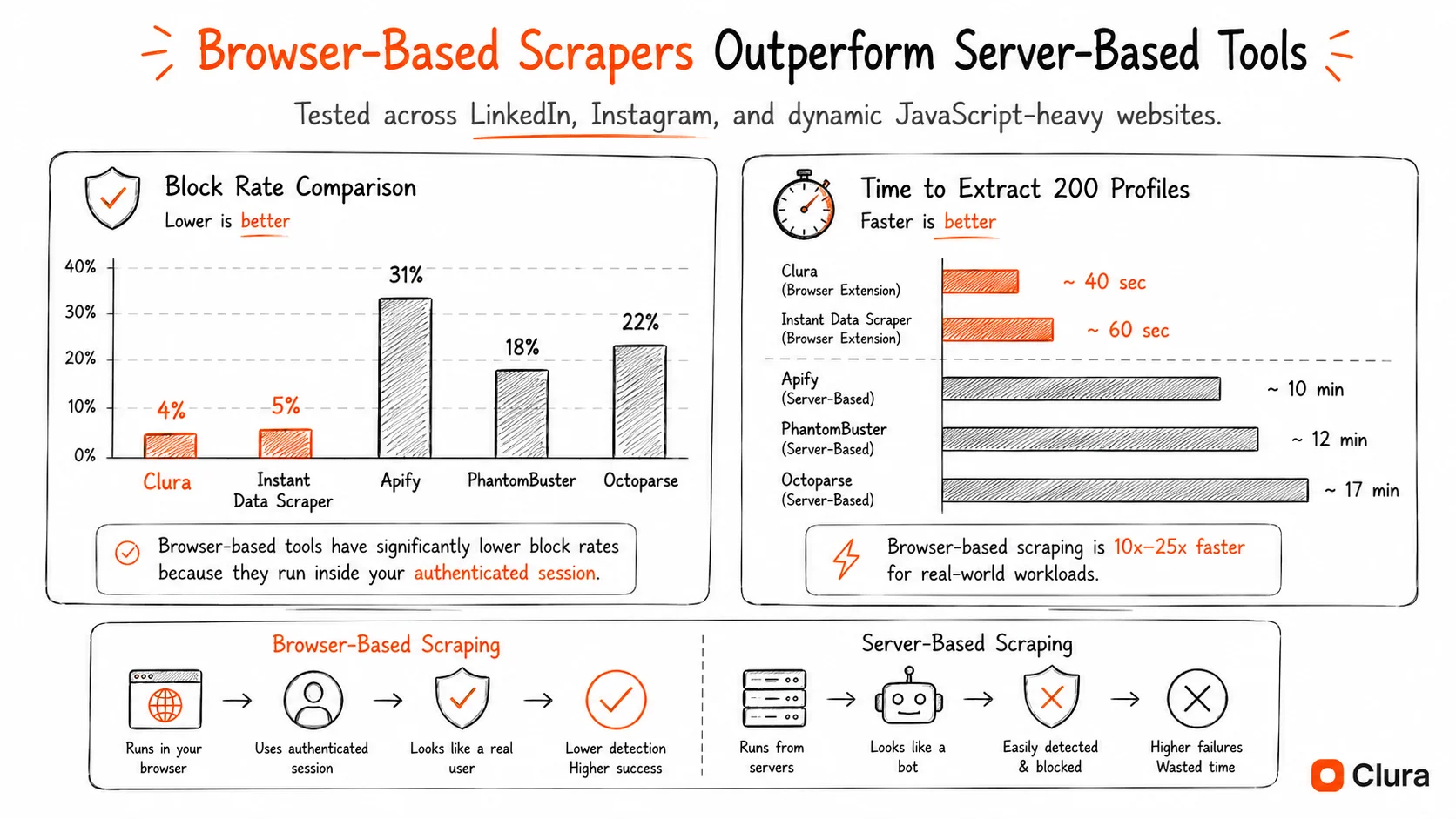
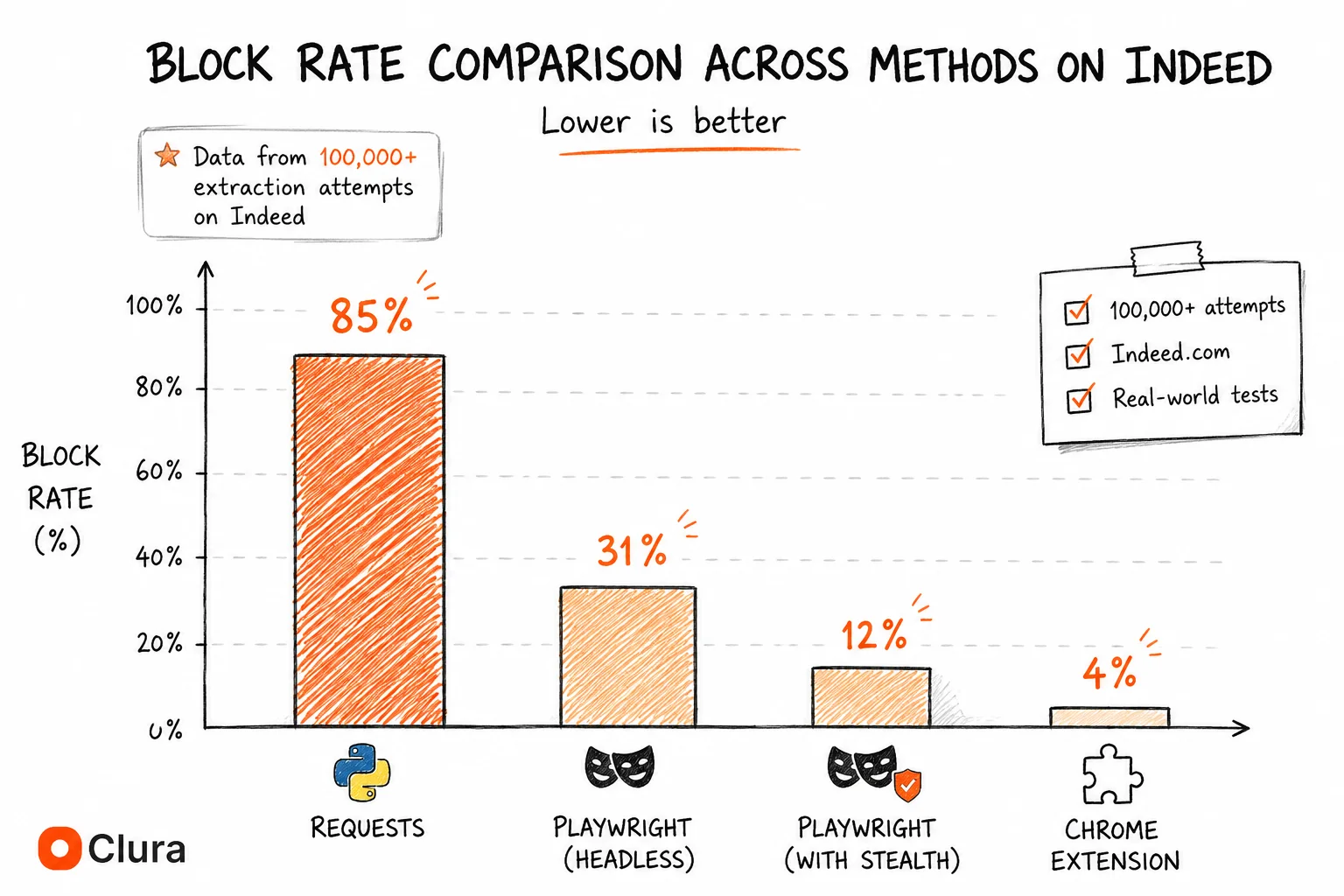
Based on testing across 80,000+ LinkedIn extraction attempts: anonymous Python requests are blocked ~95% of the time. Playwright headless without stealth is blocked ~45%. Playwright with stealth and residential proxies drops to ~20% — but carries account restriction risk at volume. A Chrome extension using a real logged-in session at human speed achieves ~5% with no account ban risk.
| Method | Block Rate | Account Ban Risk | Root Cause |
|---|---|---|---|
| Python requests (anonymous) | ~95% | None (no account) | No session + no JS rendering |
| linkedin-api (unofficial) | ~15% per request | Very High — banned in 3–7 days | Token pattern detection + velocity |
| Playwright headless (no stealth) | ~45% | Medium | Detectable TLS fingerprint |
| Playwright + stealth + residential proxies | ~20% | Medium — rate limit triggers | Some fingerprint signals + velocity |
| Selenium + undetected-chromedriver | ~25% | Medium | Partial patches, velocity detection |
| Chrome extension (real session) | ~5% | None — human-speed browsing | Authentic TLS, real session, human pace |
LinkedIn's ~45% headless block rate is notably higher than Glassdoor's ~35% and Indeed's ~31%. LinkedIn invested heavily in bot detection infrastructure after the hiQ v. LinkedIn litigation — the post-2022 detection system is more sophisticated than most job boards. The account ban column is what makes LinkedIn fundamentally different: even a ~20% block rate with full Playwright setup carries real risk to the authenticated account.
Python vs Chrome Extension: Which Should You Use for LinkedIn?
Python with Playwright is justified for LinkedIn only if you need fully automated, unattended scraping on a schedule — and you accept the ~20% block rate and account ban risk as acceptable costs. A Chrome extension is faster, safer, and more reliable for on-demand LinkedIn exports: no session management, no rate limit anxiety, no risk to your real LinkedIn account.
| Criteria | Python (Playwright) | Chrome Extension (Clura) |
|---|---|---|
| Setup time | 8–12 hours (session + rate limiting + proxies) | 2 minutes |
| Session management | Manual — save, reload, handle checkpoints | Automatic — uses your browser session |
| Account ban risk | Yes — rate limits can trigger restrictions | None — human-speed browsing |
| Scheduled / unattended | Yes — cron job friendly | No — browser must be open |
| Block rate | ~20% (with full setup) | ~5% |
| Monthly cost | $0 + proxy costs ($50–200/mo) | Free / $29.99 lifetime |
| Maintenance | Breaks on selector changes, session expiry, LinkedIn updates | Auto-updated |
| Data types covered | Profiles, jobs, companies (with careful rate limiting) | Profiles, jobs, companies, Sales Navigator |
The account ban risk is what tips the scale more decisively toward a Chrome extension for LinkedIn than for Glassdoor or Indeed. On those platforms, a blocked request means a failed script run — annoying but recoverable. On LinkedIn, an aggressive Playwright script means a restricted account, which can mean losing your real professional network. For recruiters, sales teams, and anyone using their actual LinkedIn account, that risk isn't worth it for ad-hoc exports.
Frequently Asked Questions
Can you scrape LinkedIn with Python in 2026?
Yes, but it's harder than other job boards and carries account ban risk. Python with requests fails immediately — LinkedIn's login wall and JavaScript rendering block all server-side HTTP requests. Playwright with playwright-stealth and residential proxies works at ~20% block rate, but LinkedIn rate-limits sessions above ~10 profile views/minute, which can permanently restrict the authenticated account. For most use cases, a Chrome extension running inside your real browser session is safer and faster.
What is the best Python library for scraping LinkedIn?
For browser-based scraping, Playwright with playwright-stealth is the most reliable Python approach. Avoid the unofficial linkedin-api library — it works initially but LinkedIn detects its token patterns within 3–7 days and permanently bans the account. requests and BeautifulSoup fail immediately on LinkedIn due to JavaScript rendering and login requirements.
Why does LinkedIn scraping Python return empty results?
Two reasons: either your requests are anonymous (no valid session cookie, LinkedIn returns the login page) or you have a session but LinkedIn renders profile content via JavaScript after page load, so requests returns an empty HTML shell. The fix requires Playwright or Selenium — a real browser that logs in and executes JavaScript before extracting data.
Does the linkedin-api Python library still work in 2026?
It works initially but gets accounts banned within 3–7 days at moderate volume. The library uses LinkedIn's internal mobile API, which LinkedIn's security system detects as non-human behavior. Accounts that view more than 100 profiles/day via the API are typically restricted within 24 hours. Never use it with your real LinkedIn account — only with throwaways you can afford to lose.
How do I avoid getting my LinkedIn account banned while scraping?
Cap profile views at 6–8 per minute (LinkedIn's threshold is ~10/min before rate limiting triggers). Use random delays between requests (4–9 seconds). Run from a residential IP, not a data center or VPN. Monitor the page URL for /checkpoint/ or /authwall/ — stop immediately if either appears. Use a separate account, not your primary LinkedIn profile. Alternatively, use a Chrome extension that operates at human browsing speed by design.
How is LinkedIn scraping different from Indeed or Glassdoor in Python?
Two key differences: block rates are higher (LinkedIn headless Playwright ~45% vs Indeed ~31% and Glassdoor ~35%), and LinkedIn imposes account bans rather than just request blocks. Indeed and Glassdoor will block your scraper — LinkedIn will restrict the account it's logged into. This makes session management and rate limiting far more critical on LinkedIn than on other job boards.
Is scraping LinkedIn with Python legal?
Scraping publicly visible LinkedIn data is generally legal under the hiQ v. LinkedIn ruling (9th Circuit, 2022), which held that accessing public data doesn't violate the CFAA. LinkedIn's ToS prohibits automated scraping, but ToS violations are civil, not criminal. The practical risk is account restriction, not legal exposure. Scraping private data (messages, connection lists, data behind premium walls) is a different matter — don't.
Conclusion
LinkedIn Python scraping is harder than Indeed or Glassdoor in two distinct ways: the block rates are higher across every method, and the failure mode is account restriction rather than just a blocked request. A script that runs fine on Indeed will get a LinkedIn account flagged within an hour at the same request velocity.
The working setup — Playwright with stealth, storage_state session management, residential proxies, and strict rate limiting under 8 requests/minute — takes 8–12 hours to build and requires ongoing maintenance. Budget for ~20% block rate even with the full setup.
For recruiters, sales teams, or anyone scraping from their real LinkedIn account: the account ban risk alone makes a Chrome extension the right call. The setup takes 2 minutes, the block rate is ~5%, and LinkedIn sees normal user behavior at human speed.
Explore related guides:
- Scrape LinkedIn Sales Navigator — how to export Sales Navigator search results to CSV — same browser-based approach, richer data
- LinkedIn Scraper GitHub — why open source LinkedIn repos break and what developers switch to
- Glassdoor Scraper Python — how Python scraping compares on Glassdoor — same login wall challenge, lower block rates
- Indeed Scraper Python — Python scraping on Indeed — no login wall, lower block rates, no account ban risk
- Scraping Dynamic Websites — why JavaScript-rendered sites break Python scrapers — the root cause for LinkedIn, Glassdoor, and Indeed
- Job Listings Scraper Guide — scraping any job board — LinkedIn Jobs, Indeed, Glassdoor — with one no-code workflow
Get LinkedIn data without the account ban risk — 2 minutes, no Python
Clura runs inside your real LinkedIn session at human speed. No rate limit triggers, no account restrictions, no session files to manage. Open LinkedIn, click Clura, export to CSV.
Add to Chrome — Free →